Secure Digital Communication: Modern Privacy Solutions 2025
The Evolution of Digital Privacy in 2025
As we progress through 2025, secure digital communication has become increasingly important. With cyber threats evolving and data breaches affecting many users, traditional communication methods often don't provide adequate privacy protection. Modern privacy solutions have emerged to address these challenges, offering effective approaches to keep our digital conversations secure and private.
The landscape of digital communication has fundamentally shifted from simple convenience-focused messaging to privacy-first approaches. Today's users demand not just encrypted transmission, but complete control over their digital footprint, including the ability to ensure messages disappear permanently after serving their purpose.
Key developments in modern secure communication include:
- Ephemeral Messaging - Messages that automatically self-destruct after reading
- Zero-Knowledge Architecture - Service providers cannot access message content
- Advanced Encryption - Quantum-resistant encryption algorithms
- Steganographic Privacy - Hidden messages using zero-width characters
Digital Privacy Challenges in 2025
Recent data shows that many digital communications are stored permanently by service providers, creating privacy vulnerabilities. The average person's communication data spans many years of digital history, representing a security risk if compromised. Modern privacy solutions address this by ensuring communications have defined lifespans.
Modern Privacy Technologies for Communication
The year 2025 has brought advances in privacy technology, changing how we approach secure digital communication. These innovations address key challenges of traditional messaging while providing user-friendly solutions for everyday privacy needs.
Self-Destructing Message Technology
Modern self-destructing messages go beyond simple deletion. Advanced implementations include:
- Cryptographic verification of complete destruction
- Multiple destruction triggers (time, access count, location)
- Quantum-resistant encryption during message lifespan
- Forensic-proof elimination from all storage systems
Zero-Width Character Steganography
One of the innovative privacy solutions of 2025 is zero-width character encryption:
- Messages hidden invisibly within normal text
- Undetectable to standard text analysis tools
- Multiple layers of steganographic encoding
- Compatible with all standard communication platforms
Quantum-Resistant Encryption
As quantum computing advances, privacy solutions have evolved to include:
- Post-quantum cryptographic algorithms
- Hybrid classical-quantum encryption schemes
- Future-proof security against emerging threats
- Seamless integration with existing systems
Practical Applications of Modern Privacy Solutions
Modern privacy solutions find applications across numerous professional and personal scenarios where traditional communication fails to provide adequate security:
Enterprise Security Communications
Modern businesses rely on advanced privacy solutions for:
- Executive strategy discussions that require absolute confidentiality
- Merger and acquisition communications with automatic destruction
- Intellectual property sharing with forensic-proof deletion
- Client confidential information exchange with compliance tracking
Healthcare Privacy Protection
Medical professionals utilize modern privacy tools for:
- Patient information sharing with HIPAA-compliant destruction
- Medical consultation discussions that disappear after decisions
- Research data collaboration with automatic privacy protection
- Emergency medical communications with time-sensitive destruction
Legal Practice Innovation
Legal professionals leverage advanced privacy solutions for:
- Attorney-client communications with enhanced privilege protection
- Case strategy discussions that automatically eliminate evidence trails
- Settlement negotiations with cryptographic destruction verification
- Discovery document sharing with controlled access and elimination
Implementation Strategies for Modern Privacy
Successfully implementing modern privacy solutions requires understanding both the technology and the strategic approach to secure communication:
Privacy-First Communication Strategy
Develop a comprehensive approach to secure communication:
- Classify information sensitivity levels and match to appropriate privacy tools
- Establish protocols for different types of sensitive communications
- Train team members on proper use of advanced privacy technologies
- Create verification procedures for successful message destruction
Technology Integration Planning
Seamlessly integrate privacy solutions into existing workflows:
- Assess current communication tools for privacy gaps
- Implement modern solutions with minimal workflow disruption
- Provide comprehensive training on new privacy technologies
- Monitor and optimize privacy solution effectiveness
Compliance and Documentation
Ensure privacy solutions meet regulatory requirements:
- Document privacy protection procedures for audit purposes
- Verify compliance with industry-specific regulations
- Maintain records of successful message destruction
- Regular review and update of privacy policies
Secure Your Digital Communication Today
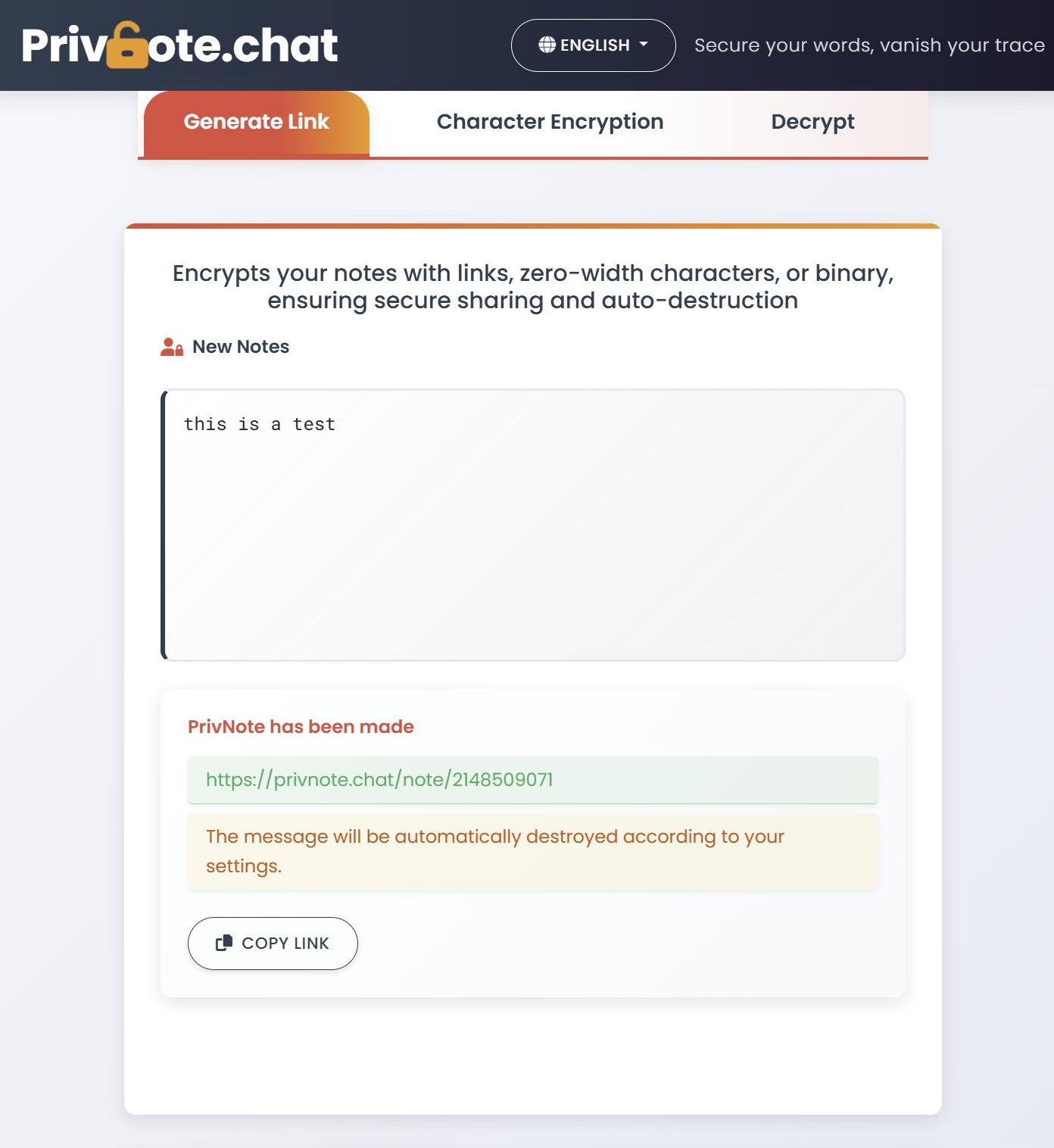
Experience modern privacy solutions firsthand. Send self-destructing encrypted notes and protect your digital conversations with cutting-edge technology.
Try Privnote FreeFuture Trends in Digital Privacy Protection
As we look toward the remainder of 2025 and beyond, several emerging trends are shaping the future of digital privacy protection:
AI-Enhanced Privacy Protection
Artificial intelligence is being integrated into privacy solutions to provide:
- Intelligent threat detection and automatic privacy escalation
- Smart content analysis for optimal encryption selection
- Predictive privacy protection based on communication patterns
- Automated compliance checking for regulatory requirements
Decentralized Privacy Networks
Emerging decentralized technologies offer:
- Distributed message storage with no central control points
- Blockchain-verified destruction for complete transparency
- Peer-to-peer encryption without intermediary services
- Community-governed privacy standards and protocols
Biometric Privacy Integration
Advanced biometric integration provides:
- Biometric-locked message access for ultimate security
- Multi-modal authentication combining voice, face, and fingerprint
- Continuous authentication throughout message interaction
- Biometric destruction triggers for automatic privacy protection
Measuring Privacy Solution Effectiveness
To ensure your modern privacy solutions provide maximum protection, implement comprehensive measurement and monitoring:
Security Metrics and KPIs
- Percentage of sensitive communications using advanced privacy protection
- Time reduction in privacy incident response and resolution
- Successful message destruction verification rates
- User adoption rates across different organizational levels
Privacy Impact Assessment
- Reduction in digital footprint exposure risks
- Improvement in regulatory compliance scores
- Decrease in privacy-related security incidents
- Enhanced stakeholder confidence in communication security
Conclusion: Embracing the Future of Secure Communication
Modern privacy solutions represent a fundamental shift in how we approach digital communication security. By embracing technologies like self-destructing messages, zero-width character encryption, and quantum-resistant cryptography, we can achieve levels of privacy protection that were impossible just a few years ago.
The key to successful implementation lies in understanding that privacy is not just a feature—it's a comprehensive approach to communication that considers the entire lifecycle of information. From creation and transmission to storage and ultimate destruction, every aspect of the communication process must be designed with privacy as the primary consideration.
As we continue through 2025, the organizations and individuals who embrace these modern privacy solutions will find themselves better protected against evolving threats while maintaining the convenience and efficiency required for effective communication.
Start implementing modern privacy solutions today and experience the peace of mind that comes from knowing your sensitive communications are protected by the most advanced privacy technologies available. The future of secure digital communication is here—and it begins with taking the first step toward comprehensive privacy protection.