End-to-End Encryption: A Complete Guide for Private Communication
What is End-to-End Encryption?
End-to-end encryption (E2EE) is a secure communication method that prevents third parties—including service providers, hackers, and even government agencies—from accessing data while it's transferred from one system or device to another. In an E2EE system, only the communicating users can read the messages. No intermediary, not even the platform hosting the communication, can access the cryptographic keys needed to decrypt the conversation.
The "end-to-end" in E2EE refers to the fact that the encryption covers the entire journey of a message, from its origin (one end) to its destination (the other end). This distinguishes it from other forms of encryption, which might only protect data during transit but allow service providers to access unencrypted data at either endpoint.
How End-to-End Encryption Works
Understanding the technical aspects of E2EE can help you appreciate its security benefits:
Key Generation and Exchange
When you initialize a secure conversation with someone using E2EE:
- Your device generates a public key and a private key.
- The public key can be shared with anyone, while the private key remains securely on your device.
- Your contact's device does the same, generating their own key pair.
- You and your contact exchange public keys, either directly or through a trusted server.
Message Encryption Process
When you send a message to your contact:
- Your device encrypts the message using your contact's public key.
- The encrypted message travels through the network to your contact.
- Even if intercepted during transit, the encrypted message appears as gibberish without the corresponding private key.
- Upon receipt, your contact's device uses their private key to decrypt the message.
Why End-to-End Encryption Matters
In today's digital landscape, E2EE has become increasingly important for several compelling reasons:
Privacy Protection
E2EE ensures that sensitive information remains confidential between you and your intended recipient. This is crucial for:
- Personal communications about health, finances, or other private matters
- Business discussions containing proprietary information
- Sharing confidential documents or credentials
- Protecting conversations from data mining for advertising purposes
Security Against Data Breaches
Even if a service provider experiences a data breach, your encrypted messages remain secure because:
- The service never has access to the decryption keys
- The encrypted data is meaningless without the private keys
- Hackers would need to compromise individual devices to access the content
Protection from Surveillance
E2EE provides critical protection against various forms of surveillance:
- Prevents service providers from being compelled to provide readable message content
- Reduces vulnerability to mass surveillance programs
- Protects journalists, activists, and others who may be targeted for their communications
Security Tip
While E2EE protects the content of your messages, it doesn't hide metadata—information about who is communicating with whom, when, and how often. For maximum privacy, consider combining E2EE with other privacy tools like VPNs or self-destructing messages.
E2EE vs. Self-Destructing Messages: Complementary Security
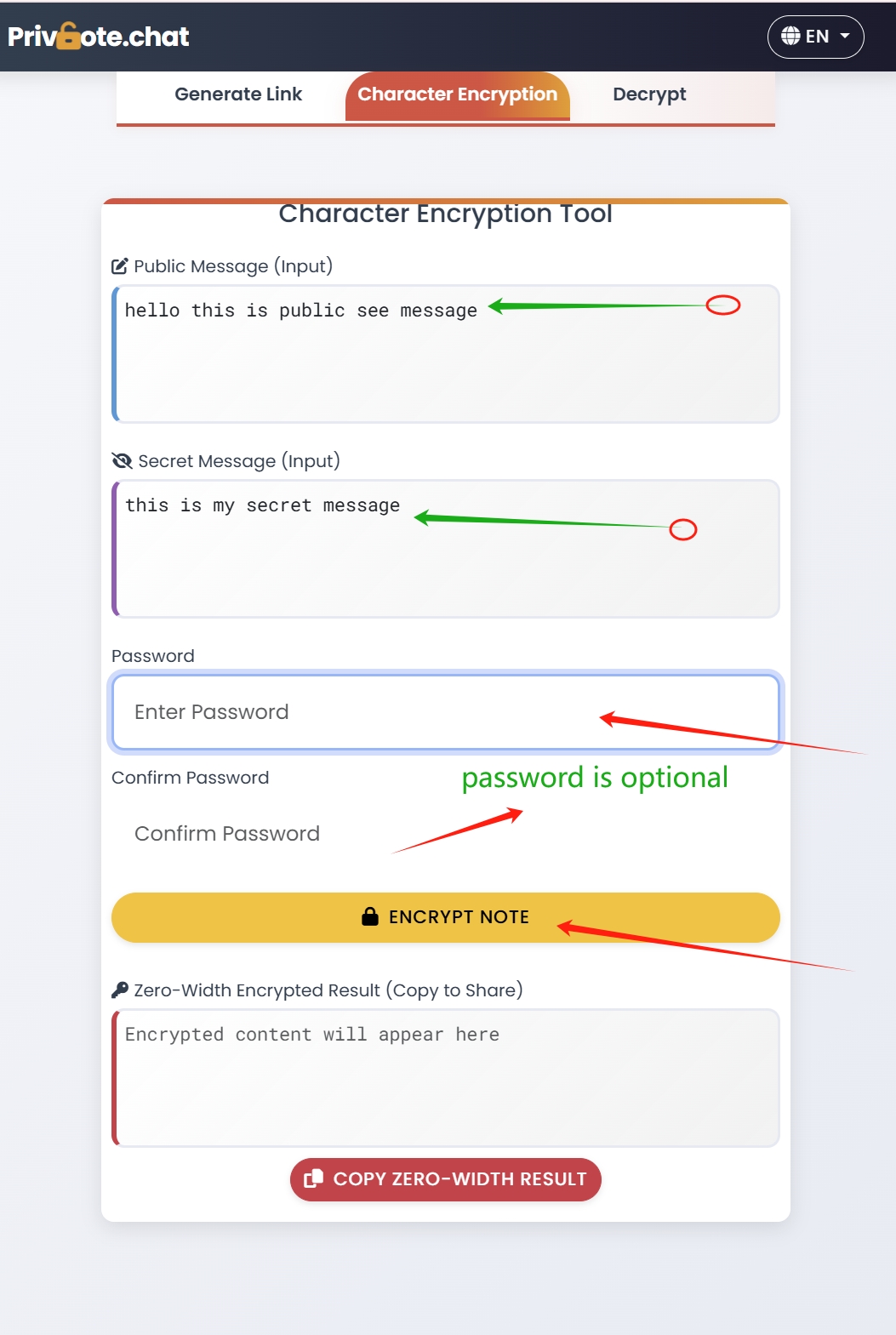
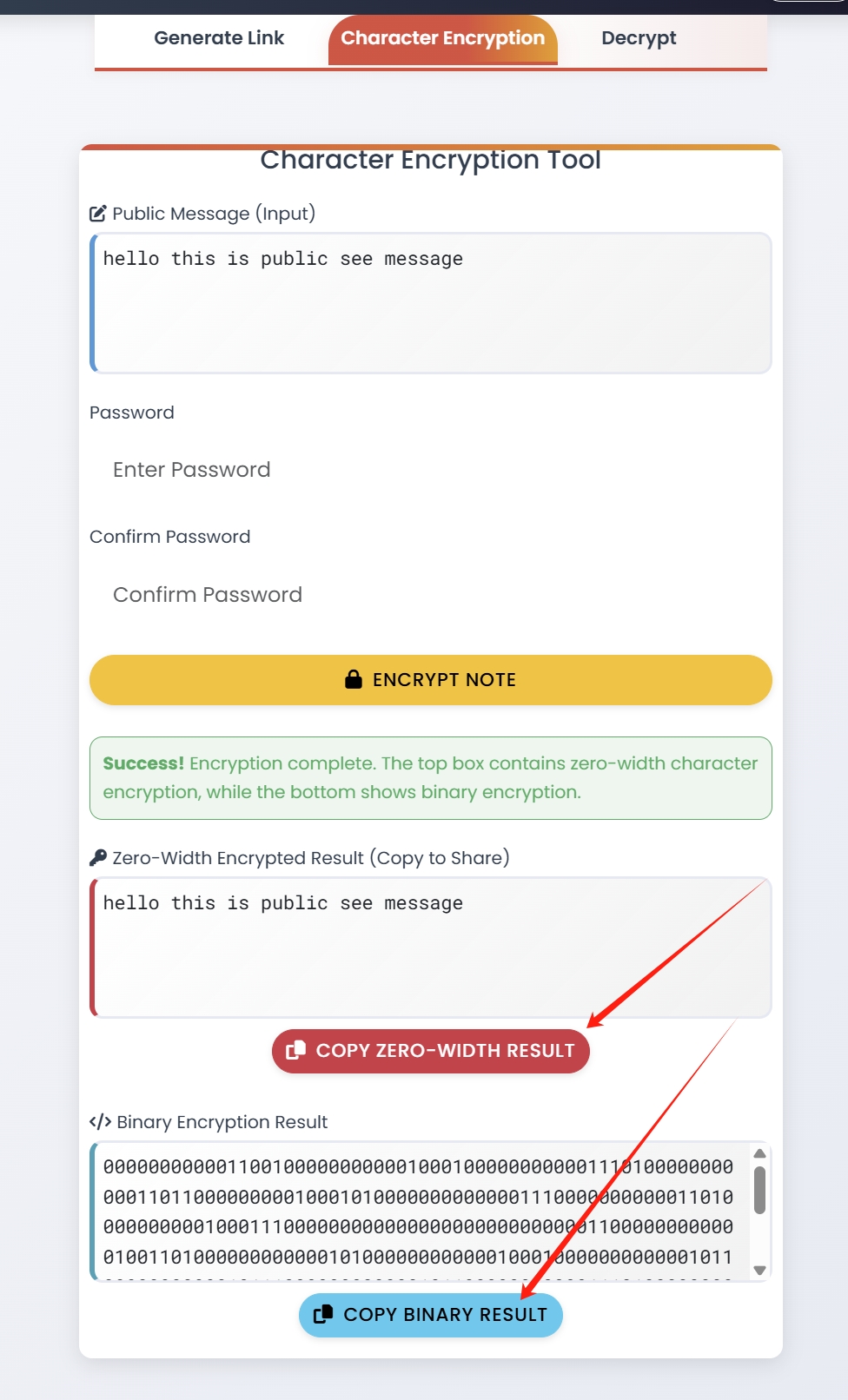
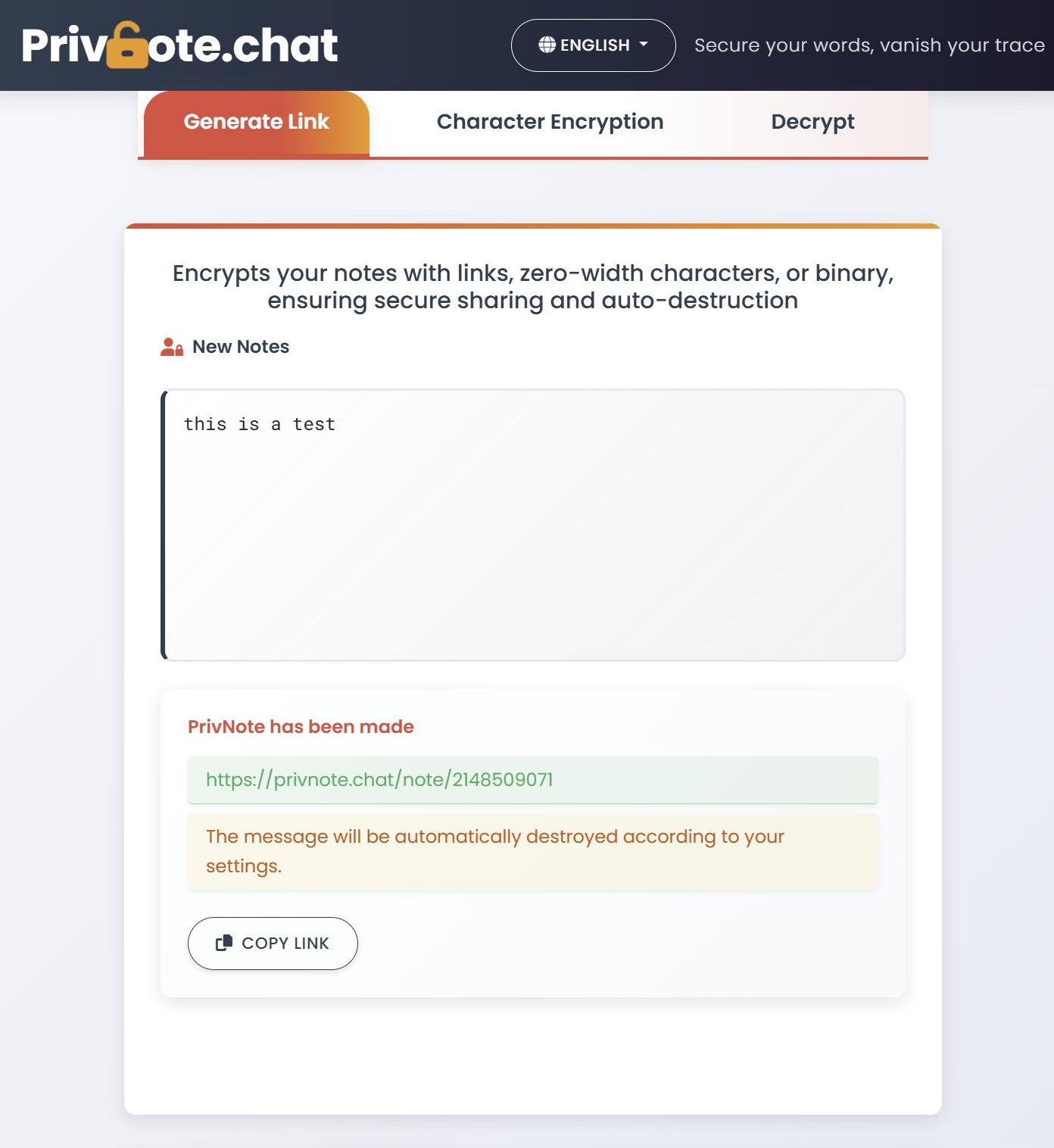
End-to-end encryption and self-destructing messages address different aspects of communication security. Let's examine how Privnote combines both approaches:
As illustrated above, Privnote encrypts messages on the client side before sending them to the server, ensuring true end-to-end encryption. Combined with automatic destruction after reading, this provides comprehensive protection:
End-to-End Encryption
Protects: Data in transit
Prevents: Interception by third parties
Weakness: Messages remain on devices indefinitely
Self-Destructing Messages
Protects: Data persistence
Prevents: Future access to message content
Weakness: Doesn't protect against interception
Using both technologies together provides comprehensive protection: E2EE secures the transmission of your message, while self-destructing functionality ensures the message doesn't remain accessible indefinitely after it's been read.
Conclusion: The Future of Secure Communication
End-to-end encryption has evolved from a niche technology to an essential component of modern digital security. As we've explored throughout this guide, E2EE provides critical protection for personal communications, business data, and sensitive information of all kinds.
In an era of increasing digital surveillance, data breaches, and sophisticated cyber threats, the role of E2EE will only grow more important. The technology continues to evolve, with new approaches being developed to address quantum computing threats and improve usability without sacrificing security.
For individuals concerned about privacy, the combination of E2EE with self-destructing messages provides a comprehensive security approach—protecting both the transmission of information and limiting its persistence after it has been read.
As users become more privacy-conscious, demand for secure communication tools will continue to rise. The companies and platforms that make security and privacy a priority will be best positioned to meet the needs of tomorrow's digital citizens.
By understanding how E2EE works, recognizing its strengths and limitations, and following best practices for secure communication, you can take control of your digital privacy in an increasingly connected world.
Your Next Steps
Ready to enhance your communication security? Here are three actions you can take today:
- Evaluate your current messaging apps and consider switching to those with strong E2EE
- Start using Privnote for sharing sensitive information that shouldn't persist
- Share this guide with friends and family to help them understand the importance of encryption
Ready to experience the benefits of secure, self-destructing messaging? Try Privnote today and add an additional layer of protection to your sensitive communications.