Burn After Reading Notes: Complete Security Guide 2025
What You Need to See: Understanding Burn After Reading Technology
In the digital age of 2025, the concept of "burn after reading" has evolved from spy movies to practical privacy technology. When you create a note that burns after reading, you're implementing a security measure that ensures sensitive information disappears completely after the recipient sees it once. This technology represents an effective approach for temporary, secure communication.
The benefit of burn after reading notes lies in their simplicity and effectiveness. After the recipient opens and reads your message, they cannot see it again—the note is permanently destroyed. This automatic destruction after viewing reduces the risk of messages being forwarded, stored, or accessed by unauthorized parties.
Key advantages of burn after reading notes include:
- Complete Privacy - Recipients can only see the message once before it's destroyed
- No Digital Trail - After reading, no evidence of the communication remains
- Prevents Forwarding - Messages cannot be shared after the initial viewing
- Automatic Security - Destruction happens without user intervention
Why 2025 Benefits from Burn After Reading Security
With data breaches affecting many records in 2024, professionals can benefit from not leaving sensitive communications permanently stored. Burn after reading notes provide risk reduction—what doesn't exist can't be stolen, leaked, or subpoenaed.
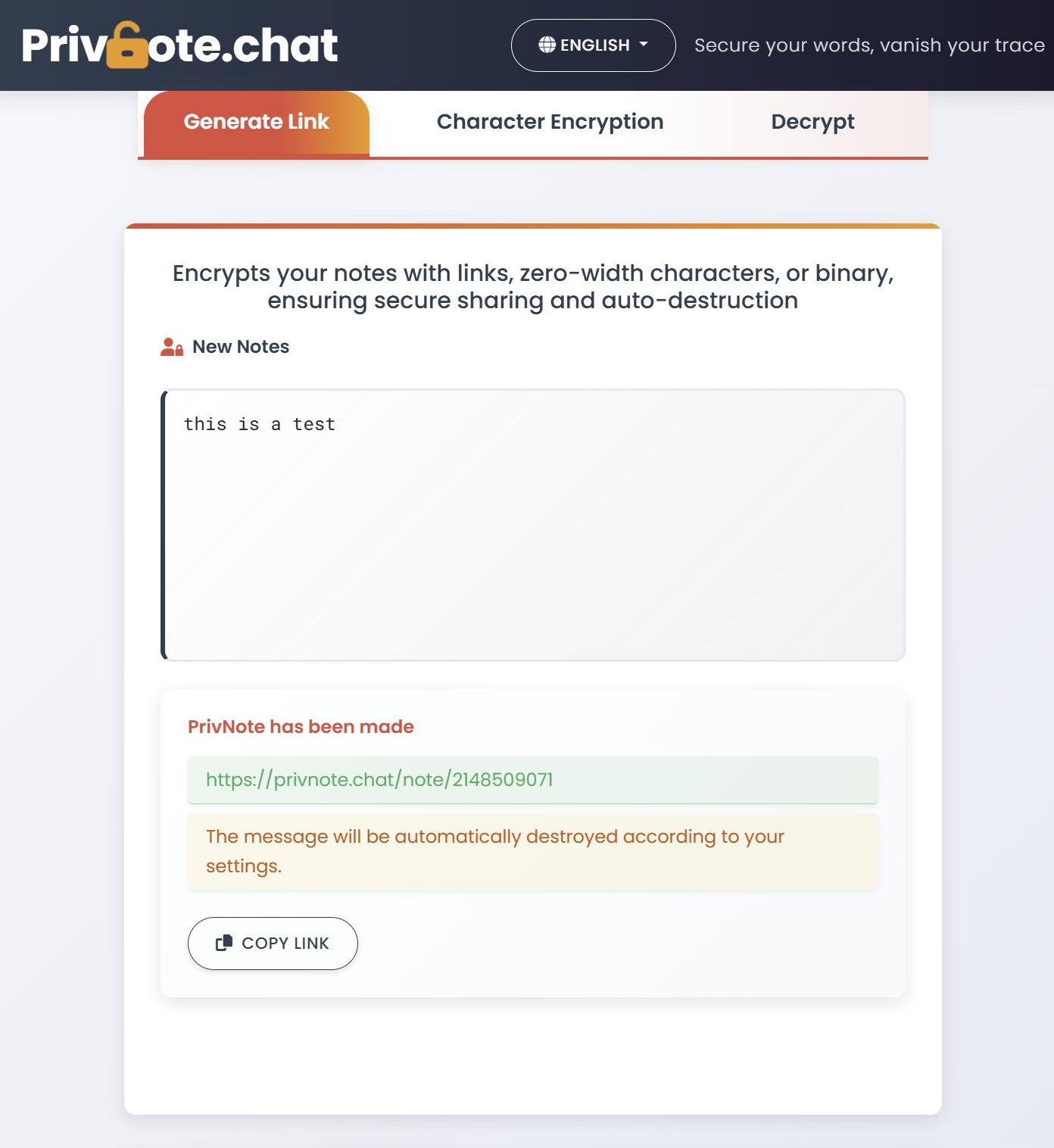
How to Create Secure Burn After Reading Notes
Creating effective burn after reading notes requires understanding both the technology and best practices. Here's what to consider when evaluating and using burn note services:
1. Choose the Right Platform
Not all burn note services offer the same security level. When selecting a platform, see that it provides:
- Client-side encryption before transmission
- No user registration requirements
- Immediate server-side deletion after reading
- Secure transmission protocols (HTTPS)
2. Compose Your Message Carefully
Since recipients can only see your message once, clarity is crucial:
- Be concise and specific in your communication
- Include all necessary details in the initial message
- Consider time zones when sharing time-sensitive information
- Avoid references that require additional context
3. Secure Distribution of the Link
The security chain is only as strong as its weakest link. After creating your burn note:
- Share the link through a different channel than usual
- Use secure messaging apps for link distribution
- Confirm receipt before the recipient attempts to open it
- Never include the link in easily intercepted communications
Professional Use Cases for Burn After Reading Notes
Understanding when and how to implement burn after reading technology can enhance your organization's security posture. Here are scenarios where you can see benefits:
Legal and Compliance Communications
Legal professionals increasingly rely on burn after reading notes for:
- Sharing confidential case details with clients
- Distributing sensitive discovery materials
- Communicating settlement terms privately
- Protecting attorney-client privilege in digital communications
Healthcare Information Exchange
Medical professionals use burn notes to:
- Share patient information while maintaining HIPAA compliance
- Distribute sensitive test results securely
- Coordinate care with external specialists
- Communicate with patients about private medical matters
Business Strategy and Competition
Corporate teams see value in burn after reading notes for:
- Sharing competitive intelligence securely
- Distributing proprietary research findings
- Communicating merger and acquisition details
- Protecting trade secrets during collaboration
Best Practices for Maximum Security
To see the full security benefits of burn after reading notes, implement these advanced practices:
Timing and Access Control
- Create notes just before sharing to minimize exposure time
- Coordinate with recipients to ensure timely access
- Use additional expiration timers when available
- Consider time zone differences for international communications
Content Security Guidelines
- Avoid including identifiable information unnecessarily
- Use coded language for extremely sensitive topics
- Break complex information into multiple separate notes
- Include context clues that only the intended recipient would understand
Verification and Confirmation
- Confirm receipt through a separate communication channel
- Establish code words to verify successful message delivery
- Use follow-up questions to ensure comprehension
- Document that secure communication protocols were followed
The Future of Burn After Reading Technology
As we progress through 2025, burn after reading technology continues evolving. Here's what security professionals should see on the horizon:
Enhanced Encryption Standards
Next-generation burn note platforms are implementing:
- Quantum-resistant encryption algorithms
- Multi-layer security with additional authentication
- Blockchain-verified destruction confirmation
- AI-powered threat detection during message creation
Integration with Business Tools
Modern platforms are beginning to offer:
- API integration with existing security infrastructure
- Single sign-on compatibility for enterprise use
- Audit trail capabilities for compliance requirements
- Advanced analytics on communication patterns
Start Using Burn After Reading Notes Today
Don't wait for a security incident to implement burn after reading technology. Create your first secure note now and see how easy it is to add this layer of protection to your sensitive communications.
Create Secure NoteConclusion: Security You Can See
Burn after reading notes represent more than just a security tool—they're a paradigm shift toward intentional privacy. In 2025, as digital threats continue evolving, the ability to communicate sensitive information that automatically destructs after viewing provides peace of mind that traditional messaging simply cannot match.
By implementing burn after reading technology, you're not just protecting today's communications—you're future-proofing your privacy strategy. When sensitive information burns after being seen, you eliminate the long-term risks associated with permanent digital storage.
Remember: the most secure communication is the one that no longer exists after serving its purpose. Start using burn after reading notes today and see the difference that true privacy technology can make for your professional and personal communications.